Polymorphic Extensions: The Sneaky Extension That Can Impersonate Any Browser Extension

Download our Browser Extensions Whitepaper
Want to stop similar extension-based attacks? Learn the best practices for defending your enterprise against malicious extensions in our guide.
Try Enterprise BrowserHow It Works
Phase 1: Attacker Prep & Social Engineering
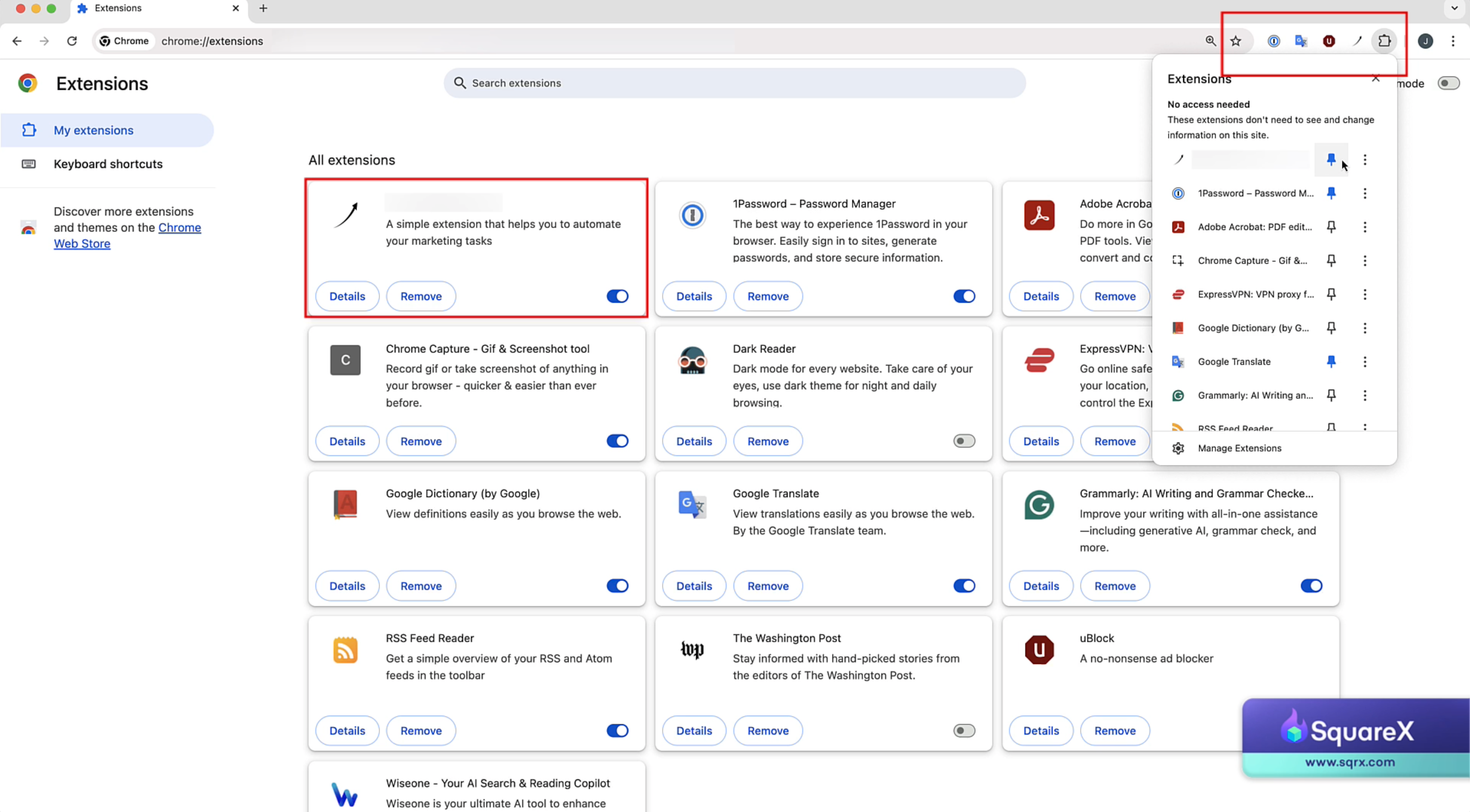
Phase 2: Identifying the Target Extension
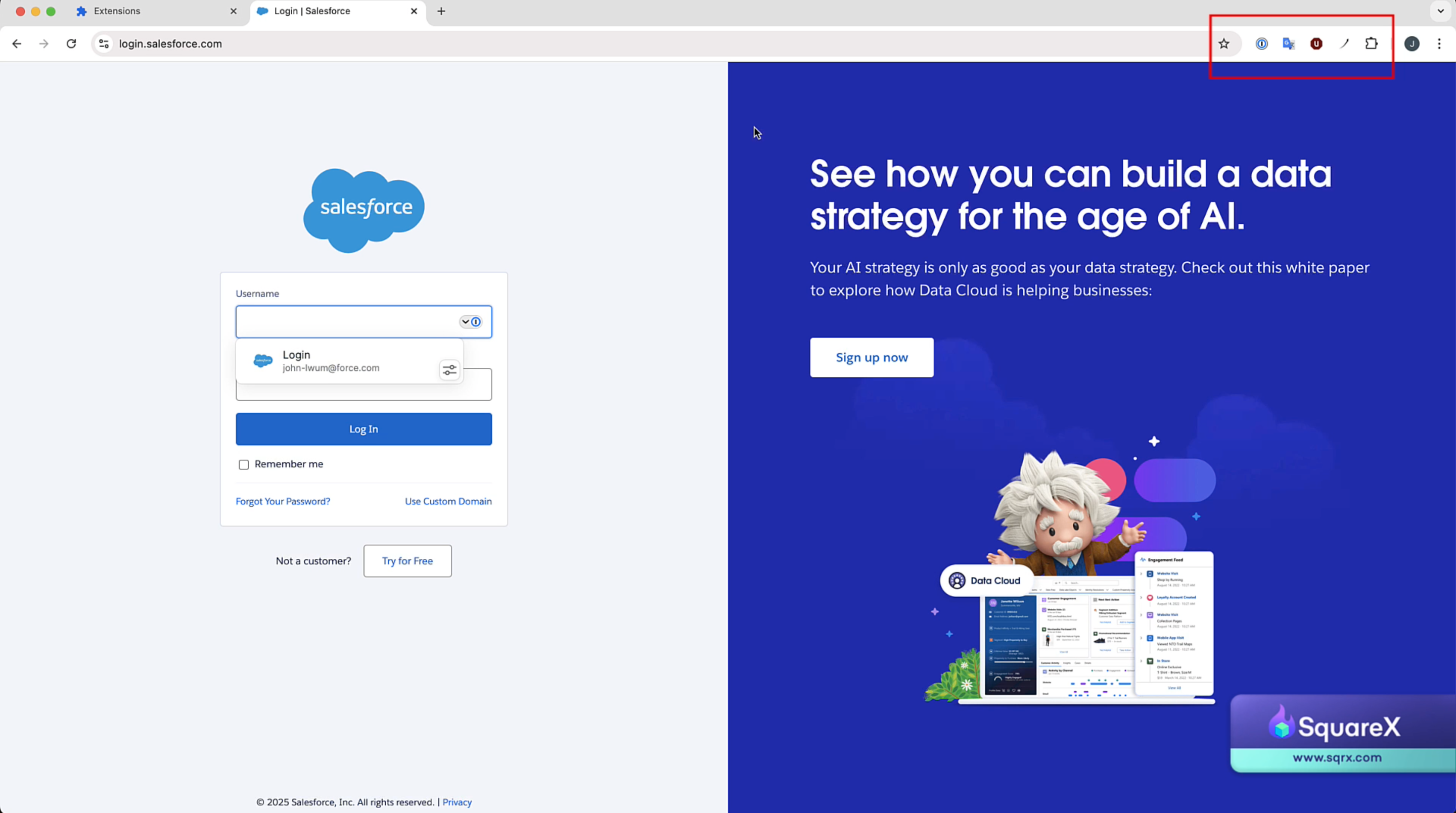
Phase 3: Impersonating the Target Extension
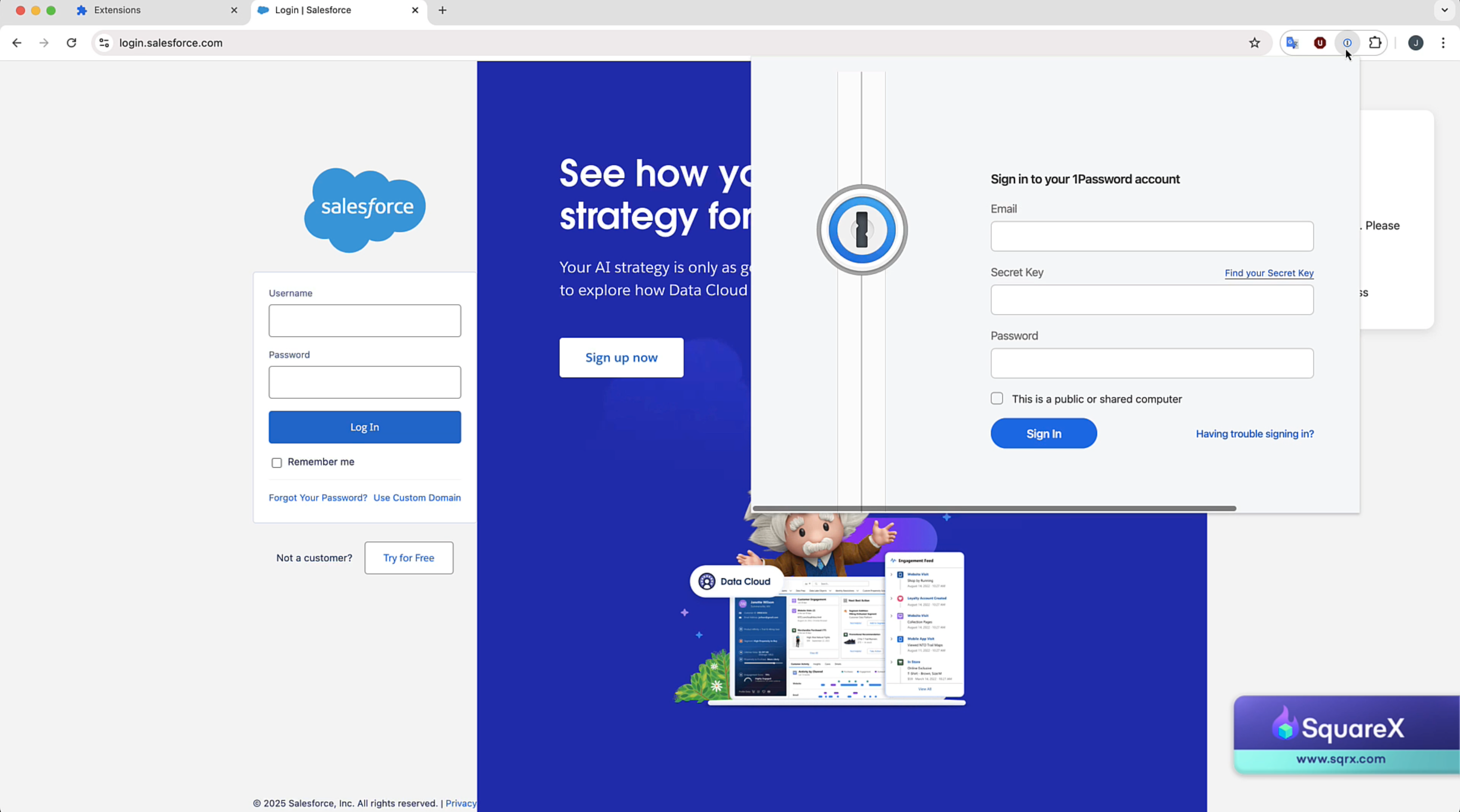

Phase 4: Impact
Watch the Attack Demonstration
"No bug to patch"
Chrome's flawed extension design
Polymorphic extensions can exist because attackers can change icon & HTML to mimic other extensions at runtime without users being notified.
With polymorphic extensions, it's clear that permission-based policies and static code analysis are no longer sufficient to defend against malicious extensions. Instead, only a browser-native security tool that dynamically analyzes extension behaviour at runtime can stop such attacks.
User Trust In Visual Cues
Users rely on visual cues such as icons to identify the what they interact with, and mostly interact with pinned extensions. Attackers take advantage of this implicit trust in visual cues – polymorphic extensions don't raise victims' suspicion until it's too late.
The Solution: Browser Detection and Response
Given that these extensions operate fully in the browser and cannot be identified by permissions or involved sites, it can only be tackled with a browser-native solution that understands the runtime behaviour of each extension. SquareX's Browser Detection and Response solution comes with a proprietary extension analysis engine with several main components:
- Highly Granular Extension-based Policies
- Advanced Extension Static Analysis
- Dynamic Analysis
- Browser Extension Policy Library
- Extension Risk Scores
- Shadow SaaS & OAuth Access Control
Click below to request a pilot, or contact us at founder@sqrxdevops.com to learn more.